Container escape attacks rose 700% between 2020 and 2021. Simultaneously, the time to detect a misconfigured container using scanning tools like Masscan fell to an average of just five hours, with 50% occurring in less than an hour.
While crypto-mining appears to be the goal of most container escape attacks – with resource hijacking occurring in 90% of reported incidents – new, deeper objectives have begun to appear as well. In all likelihood, most attackers use crypto-mining as a way to ensure some measure profitability from each attack while attempting to gain a firmer foothold and escalate privileges to escape from the container to the host machine.
Nevertheless, regardless of the purpose of the attack, the writing on the wall is clear. In today’s increasingly containerized development environments – encompassing approximately 50% of all new applications – you cannot set up a container today and expect to secure it tomorrow.
With both container adoption and misconfigurations on the rise, the legion of misconfiguration possibilities seems to be pushing against the lightweight speed and utility of containers for continuous deployment. About 94% of respondent users reported a serious security incident involving container environments in the last 12 months and 69% of those incidents involved misconfigurations.
Meeting the Challenges of Container Security with Universal Tracing
By design, container environments are ephemeral, coming and going with greater frequency than virtual machines. While this collapsibility serves the speed of continuous deployment, the payoff comes in diminished visibility and monitoring. For cloud engineers overseeing the secure configuration of these structures and the pace of deployment, container management is increasingly becoming a dilemma of balancing configuration security concerns and keeping the pipeline moving.
Taking a step back from the approach of trying to anticipate all possible vulnerabilities, Spyderbat offers cloud architects an alternative container management strategy that both eases the meticulous fine-tuning configuration process and improves overall container security effectiveness. As seasoned experts in DevOps management know, today’s decentralized cloud environments have made committing to catching everything in advance an outdated luxury of simpler times.
Spyderbat’s paradigm-breaking alternative approach shifts security focus from anticipation to enabling teams to detect and neutralize real, successful exploits as they happen. Your complex multi-cloud configurations don’t have to be perfect – which they likely can’t be even under the best of circumstances – if attackers attempting container escapes can be stopped in the process before they ever breach the actual machine host.
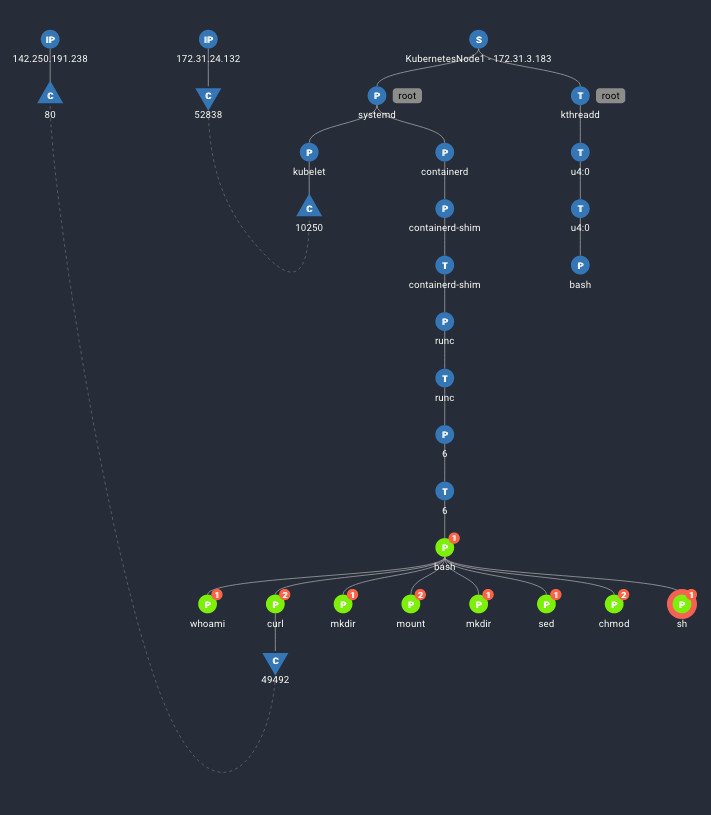
To make this enhanced security response possible, Spyderbat employs universal tracing on the totality of system activities, creating runtime, system-wide visibility into the entirety of your environment in real-time. At the user end, all processes, system calls, network connections, and user sessions appear in a visualized trace of activities based on their causal relationships – called the Universal Causal Graph (UCG). With an elevated and contextualized view of activity across systems – including containers – security teams can confidently distinguish real exploit behavior from other system anomalies that trigger false positive alerts.
In the trace, we see Spyderbat capturing a container escape.
- The blue nodes reflect activity on the host.
- The green nodes reflect activity in the container.
After gaining shell access on the container, the attacker executes commands on the file system to mount a temporary folder, manipulating the mount table to drop the user to a shell on the host itself.
Confident Runtime Security with Spyderbat
With real-time visibility into what happens as it happens across your environment – and not behind triage and investigation cycles – everyone in your organization can hold down the peddle of rapid deployments without the anxiety of exposure to unanticipated vulnerabilities.
To get started for free and experience runtime security firsthand, contact Spyderbat today.